IAM Simplified: Securing Your Cloud Infrastructure
A Comprehensive Guide to Identity and Access Management on AWS
Have you ever wondered what would've happened if every person of the organization is given the root access of the organization's AWS account? It would be a chaos right? Anybody can mess up with the resources. They might mistakenly create, update or even delete resources. This has to be avoided and only few employees must be given the privilege of root access and others should have a limited access to the resources. The AWS service that provisions this is IAM.
AWS IAM (Identity and Access Management) is a service provided by Amazon Web Services (AWS) that helps you manage access to your AWS resources. It's like a security system for your AWS account.
IAM allows you to create and manage users, groups, and roles. Users represent individual people or entities who need access to your AWS resources. Groups are collections of users with similar access requirements, making it easier to manage permissions. Roles are used to grant temporary access to external entities or services.
With IAM, you can control and define permissions through policies. Policies are written in JSON format and specify what actions are allowed or denied on specific AWS resources. These policies can be attached to IAM entities (users, groups, or roles) to grant or restrict access to AWS services and resources.
IAM follows the principle of least privilege, meaning users and entities are given only the necessary permissions required for their tasks, minimizing potential security risks. IAM also provides features like multi-factor authentication (MFA) for added security and an audit trail to track user activity and changes to permissions.
By using AWS IAM, you can effectively manage and secure access to your AWS resources, ensuring that only authorized individuals have appropriate permissions and actions are logged for accountability and compliance purposes.
Overall, IAM is an essential component of AWS security, providing granular control over access to your AWS account and resources, reducing the risk of unauthorized access and helping maintain a secure environment.
Components of IAM
Users: IAM users represent individual people or entities (such as applications or services) that interact with your AWS resources. Each user has a unique name and security credentials (password or access keys) used for authentication and access control.
Groups: IAM groups are collections of users with similar access requirements. Instead of managing permissions for each user individually, you can assign permissions to groups, making it easier to manage access control. Users can be added or removed from groups as needed.
Roles: IAM roles are used to grant temporary access to AWS resources. Roles are typically used by applications or services that need to access AWS resources on behalf of users or other services. Roles have associated policies that define the permissions and actions allowed for the role.
Policies: IAM policies are JSON documents that define permissions. Policies specify the actions that can be performed on AWS resources and the resources to which the actions apply. Policies can be attached to users, groups, or roles to control access. IAM provides both AWS managed policies (predefined policies maintained by AWS) and customer managed policies (policies created and managed by you).
Practical implementation
Firstly, sign in to your AWS account as a root user and search for the IAM service.
Creating a User and Providing Authentication :
Under access management, navigate to "Users" and click on "Create user." Provide the user name and grant the user access to the console by checking the given box. Then, select the option "I want to create an IAM user." For the password, choose the auto-generated option, as you need not burden yourself with creating the password. Additionally, users can change the password themselves once they log in. Enable the "Users must create a new password at next sign-in - Recommended" option. Click on the "Next" button to proceed to setting permissions.

For now, let's only authenticate the user without providing any authorization (attaching no policies or permissions). Keep this step as it is and click on "Next." We want to see what a user can do without any authorization. The user will only be able to access the AWS account, and they won't be able to create, update, or delete any resources.
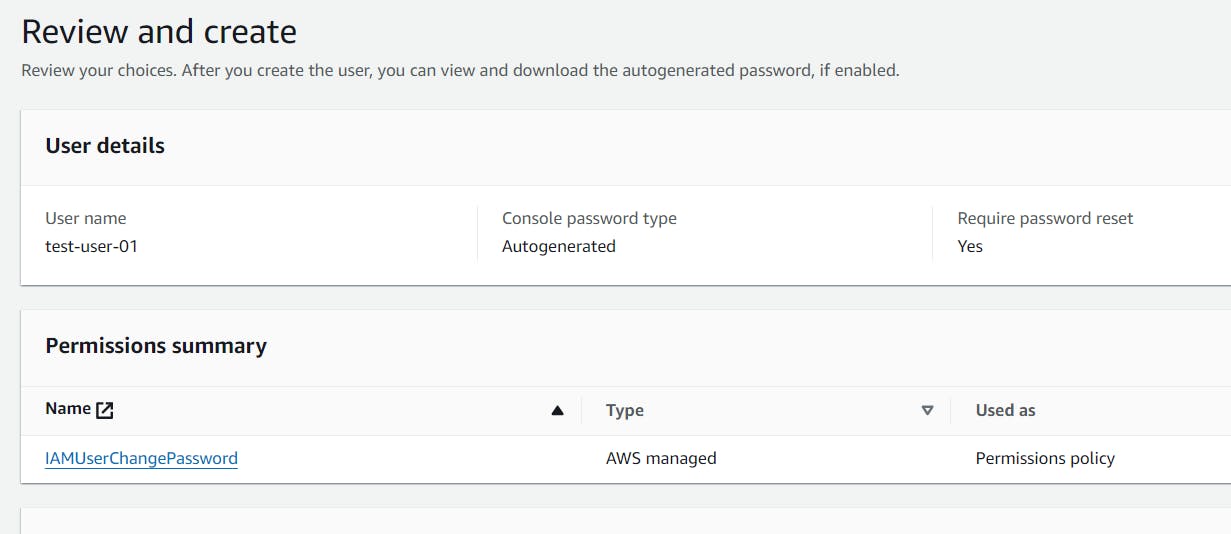
Since the user needs to reset their password upon logging in, AWS assigns the IAMUserChangePassword policy by default, as it is necessary for the user to change their password.
Click on Create user.
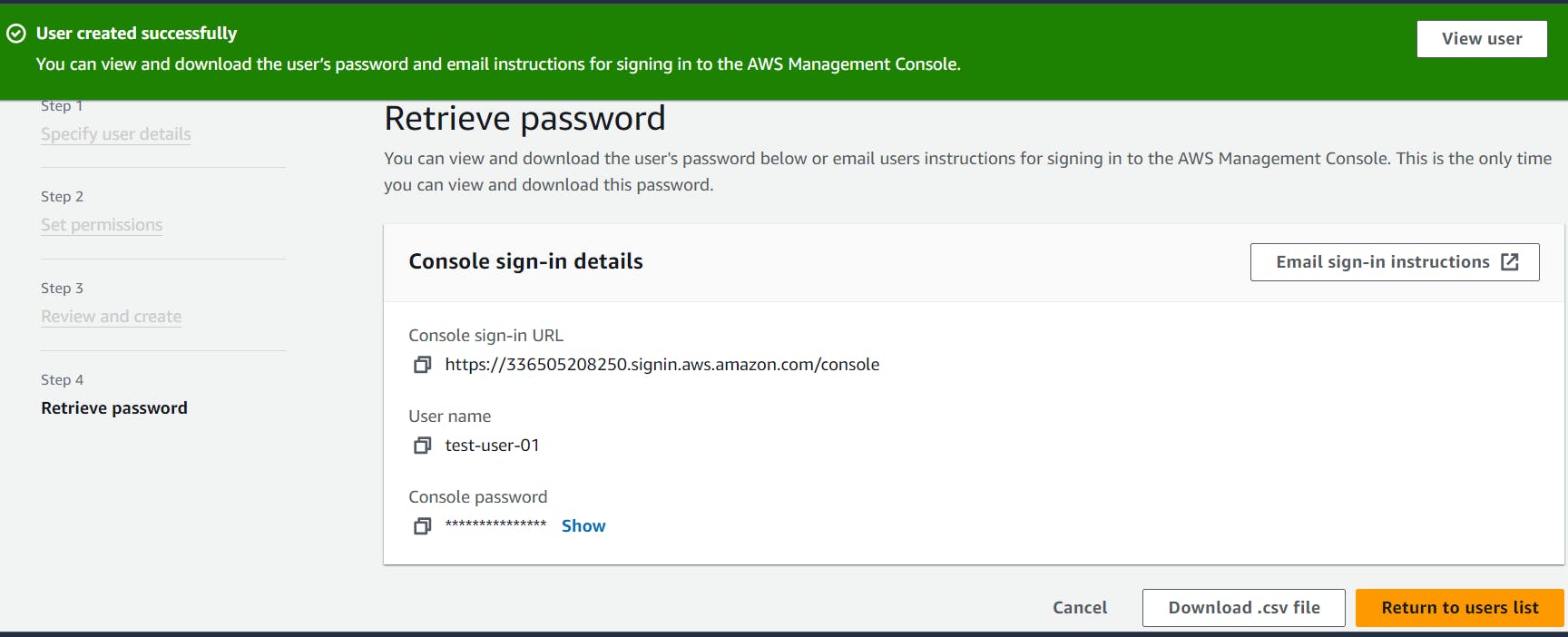
You can now view and download the user's sign-in instructions and password for accessing the AWS account. You can either copy the sign-in details or download the CSV file to share with the user. Also, you can now view the user you created in the users list.

Next, access the account as an IAM user. Sign out from the current account and sign in as the IAM user using the provided sign-in details.
The account ID is the number in the sign-in URL given.
After signing in and changing your password, you enter the console. Now, let us try to list or create or delete resources and see what we get.

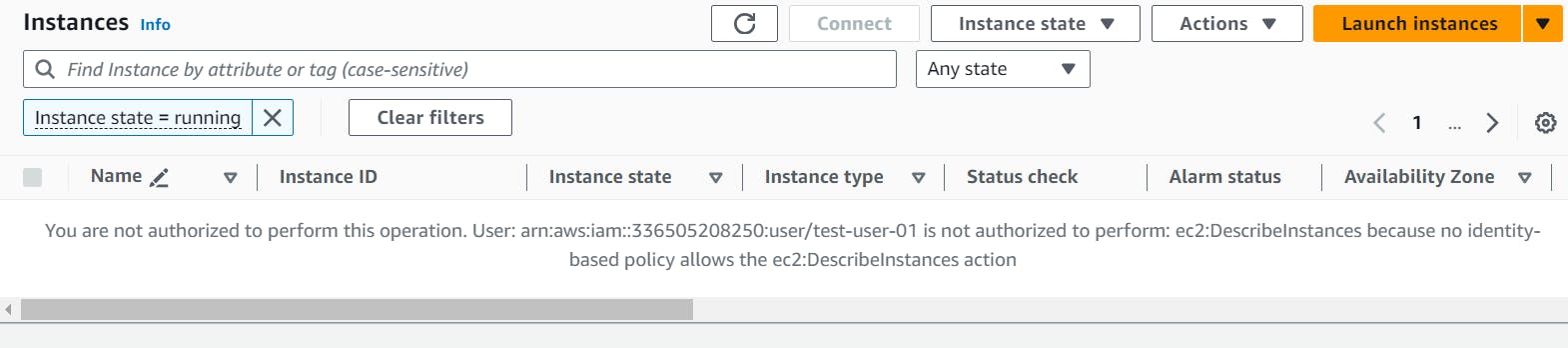
we are encountering an API error and a message indicating that the user is not authorized to access these resources
To get authorization, it is necessary to apply policies to the user. To do this, sign into the console as the root user once again and proceed to apply the required policies
Adding Permissions to an IAM User :
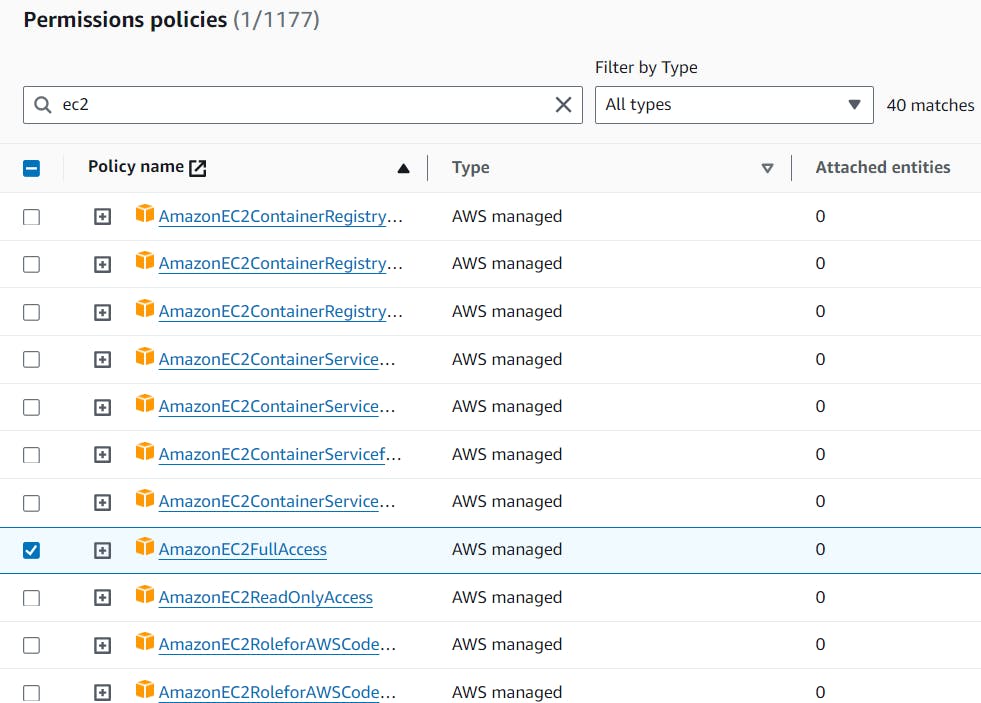
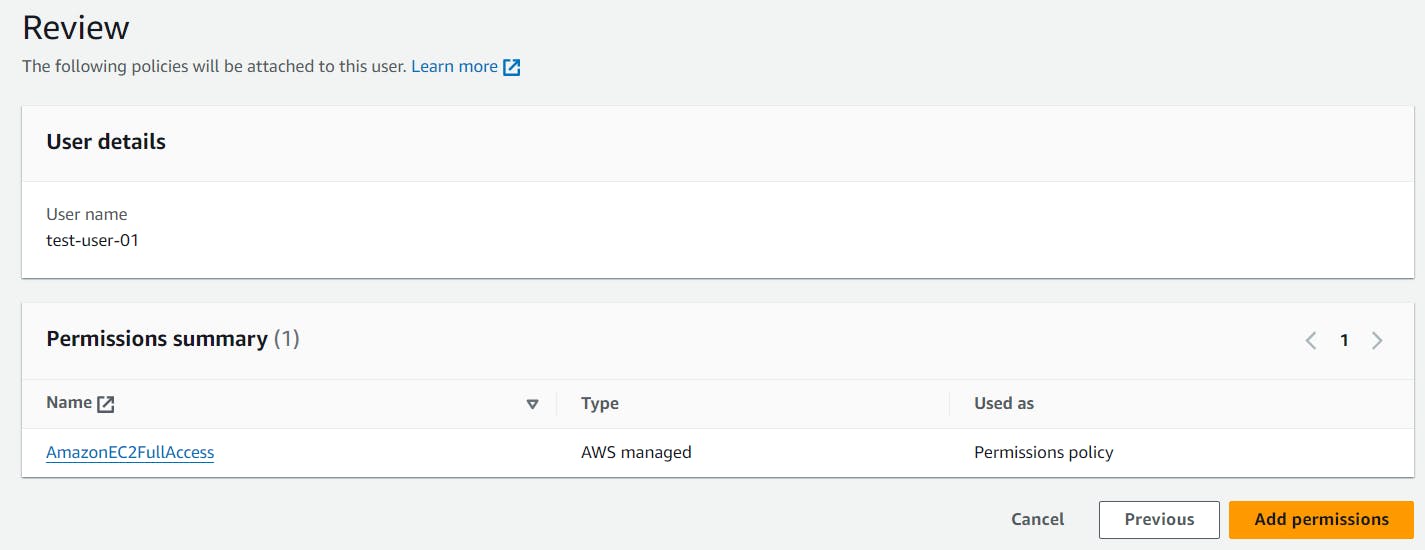
Under IAM, navigate to the "Users" section and select the specific user. Then, under "Permissions policies," click on "Add permissions" and choose "Attach policies directly." You can then select one or more managed policies to attach to the user or create a new managed policy. After making the selections, proceed by clicking "Next" to review the list of policies to be attached and then choose "Add permissions" to apply the changes.

Let us give Full access to the EC2 instances. By applying the AmazonEC2FullAccess policy.
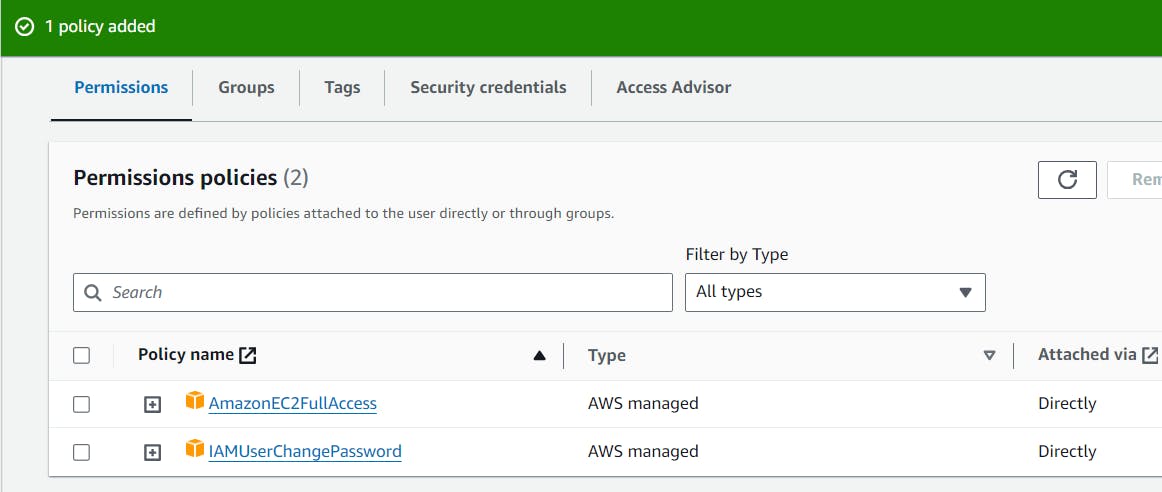
Now sign in as IAM user and try to access EC2 instances.

With full access to the EC2 instances, you can now list, create, or delete instances.
Conclusion
In conclusion, AWS IAM (Identity and Access Management) is a crucial service provided by Amazon Web Services for managing access to AWS resources. It allows for the creation and management of users, groups, and roles, and the definition of permissions through policies. By following the principle of least privilege, IAM ensures that only necessary permissions are granted, minimizing potential security risks. Additionally, features like multi-factor authentication (MFA) and an audit trail enhance security and accountability. Through IAM, organizations can effectively manage and secure access to their AWS resources, reducing the risk of unauthorized access and maintaining a secure environment. Overall, IAM plays a vital role in ensuring the security and integrity of AWS resources and is an essential component of AWS security.